my apologies for the long screenshot. i had purchased adguard’s vpn service for five years since its primary adguard service is well know in the iapple ecosystem.
on android, though, their app appears to send data to a lot of third-parties. has it always been this compromised? am i a fool to go for their vpn services as well?
How exactly are you using the duckduckgo app protection and a vpn simultaneously? DDG sets itself up as a local vpn to be able to track outgoing traffic, and Android doesn’t support concurrent connections. Or is that what adguard does in the background while not active?
you’re correct, it’s what the adguard app gets up to in the background.
the two vpns are not concurrently active.
After installing AdguardVPN and testing it against Exodus this is what I got:
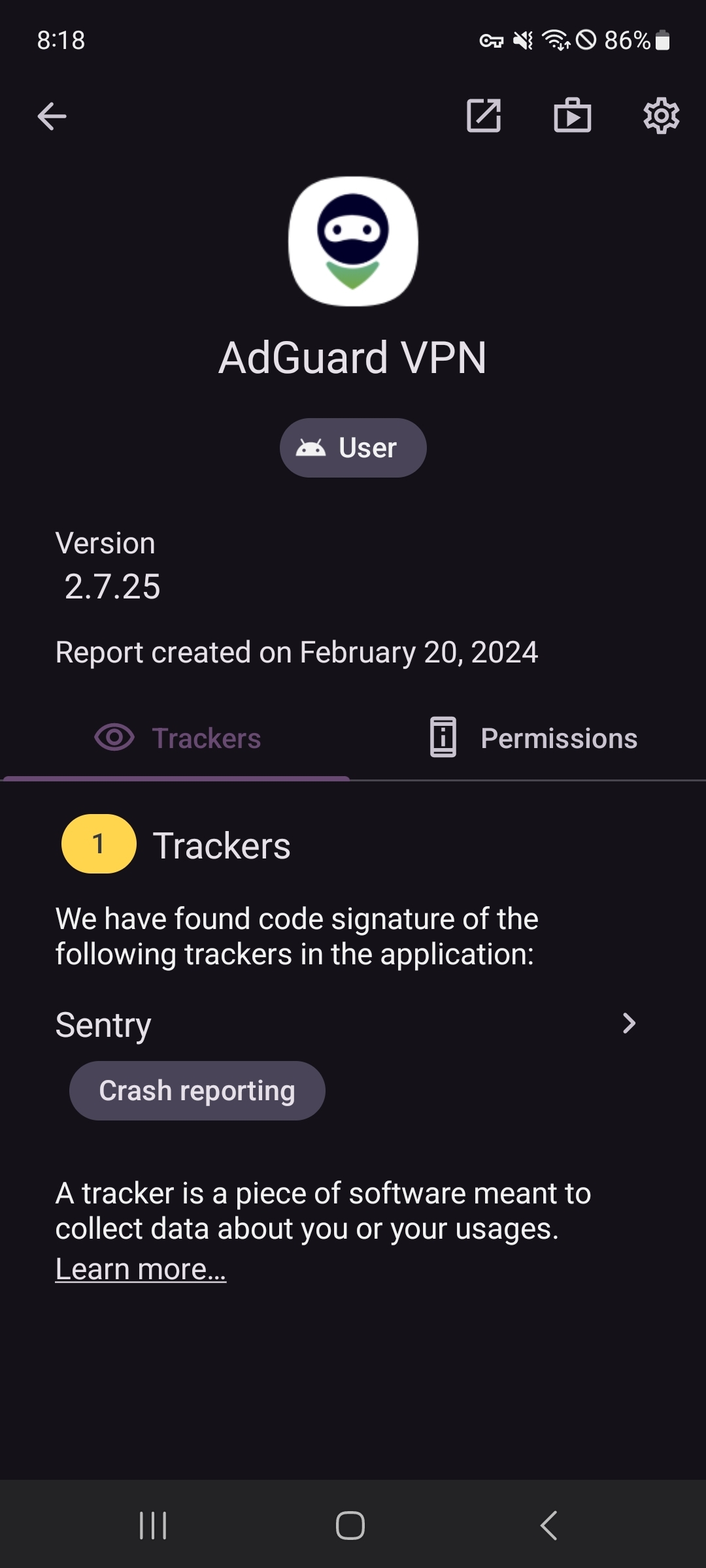
would you have done this with the ad guard vpn deactivated but the app still running in the background?
I’ve been using the app for a few montha now and it’s only today that it got flagged in the DDG report. it’s not shown up before.
Hey I gave it a second try with another tool: PCAPdroid and I’m not sure what I’m looking at … Adguard VPN seems effectively to send a lot of traffic to strange DNS requests…
Just by opening the app and loggin in a fake account I got over 200 requests…

I’m not an expert but those requests seem sketchy !!!
So at this point you’re still not connecting the VPN or anything? This is just after you log in?
Yes :) just after I login ! PCAPdroid doesn’t allow a VPN connection.
PCAPdroid doesn’t allow a VPN connection.
Could that be why the TCP status on those requests is Closed?
Edit: I’m remembering that some VPN services use users devices as a server of their own, proxying connections for other users on another service. I don’t know what’s going on here, but if you don’t have Tiktok and Snapchat both installed then I’d say that’s likely what’s going on. I’ve never used AdGuatd, there are much better VPN services.
I’m gonna say you have Tiktok and Snapchat installed on your phone? The rest of those are just random services (CDNs, ads, analytics, bug reporting, etc) that background apps (some are from Tiktok and Snapchat, but tons of apps use the same ones) are connecting to.
Set up NextDNS on your phone without any VPN running and odds are you’ll see the same.
wow. this is good detail, indeed!
so is this an app one should avoid using, then?
I would say Yes. If you are on android give PCAPdroid a try and see it by yourself.
I tried this but can’t reproduce your results. AdGuard doesn’t seem to be sending any weird DNS or tracking requests on my phone.
I’m fairly certain you’re seeing some kind of false positive, but I don’t quite know what’s going on exactly.
Selling? Probably not.
But I used NetGuard to see specific requests that the AdGuard VPN app made. Then I downloaded AdGuard VPN and opened it. Without even logging in, it pinged:
- dns.google
- dns.alidns.com (Alibaba)
- 2400:3200:baba::1 (Alibaba again)
- cloudflare-dns.com
I don’t know why it feels the need to ping so many DNS servers before you even type a username, but it does.
You are using that Duckduckgo thing which is not a reliable source of information.
I would be interested in what a “tracking attempt” would look like.
Your VPN sees EVERYTHING you connect to, if you use HTTPS that is not a big deal but can help target stuff to your usage.
If it is tracking or just traffic passthrough is decided on their servers, which no weird Duckduckgo app can access.
i get what you’re saying, but the vpn was inactive when the app sent these requests. DDG was active at the time and using the VPN slot.
so it isn’t the vpn functionality, per se, of the app that’s doing anything here.
Thanks, I think it is very relevant to understand how this DDG VPN “tracker blocking” works.
If it is about an app sending requests to lots of domains, this may have many reasons. For example it could check the IP addresses of all these tracking serverers to block apps from communicating with them via IP and not URLs.
This would be a reason that a trusted app connects to tracking servers to update their internal filterlist.
This “known to collect” seems to be unrelated to the actual connection, just “this service often collects data about x”.
If this is true, that is HIGHLY misleading and please update your post to explain that possibility.
this is a possibility. one that i haven’t accounted for.
but is there any literature that verifies this? the closest I’ve found in context is this page, and I’m not able to resolve what you’re saying with whats on there: https://adguard.com/kb/general/ad-filtering/filter-policy/
i don’t have enough info yet to update the post with this conjecture.
You need to contact them, if they connect to known to-be-blocked sites to get their IPs.
Googerteller does this:
Note: Find it ironic or not, but to query the list of all Google IPs/subnets, this needs to contact one Google domain, actually. (That request does not emit a sound, though.)
And I would ask DDG how their “tracker blocker” works and if it would also block such requests.0
The VPN isn’t generating the requests. Other apps on your device are. Run a VPN for a while and look at data usage by app. I guarantee your VPN app will be the highest (all the other apps data gets funneled through the VPN).
the vpn wasn’t connected at the time these requests were sent. that’s how DDG captures these requests, by using the vpn slot itself. these requasts were sent by the adguard app in the background when it was deactivated.
the data sent to third-party ttrackers had nothing to do with the vpn functionality or of other apps funneling their data through it.
this observation has also been corroborated by another user using other means elsewhere in the comments. do give it a dekko, too.
Don’t use proprietary software as it is not good for privacy or freedom
Pixels ?
it’s an upload limitation here, i think?
Nop it won’t just simply upload atleast that’s my experience
i dont know why it’sa at such a low resolution here. it’s fine on my phone.
here, ill try uploading a fresh non-stretched single-screen screenshot to see if the size was the issue.
(i don’t know how it will turn out myself until after i post it.)

Yeah it looks good now
Use F-Droid apps. Since most Google store apps contain trackers. Then use ClassyShark to check trackers.
From what I see, your screenshot tells what adguardVPN blocked. Each app shown in adguardVPN seems to send a lot of things.Maybe time to switch to alternatives if you are concerned about telemetry and personal data?My bad, see answer below !
No that’s the duckduckgo app which is blocking outgoing connection attempts from adguard.
What I don’t know is whether those are actual connection requests of adguard, or whether they came from any other apps and were routed through the VPN and that’s why they ended up on this list.
I’m not quite sure how the duckduckgo app actually works to track/block those requests.
DuckDuckGo uses the VPN slot to work, so if they’re using it to block trackers, they can’t be simultaneously using an actual VPN.
Yep, exactly my thoughts after reading how it works. Actually installed DDG as well to double check, and as expected I can’t run it simultaneously to my VPN.
you are correct. activating one switches off the other. but the adguard vpn app still runs in the background even with its own vpn deactivated – and that’s when these requests were caughtin DDG’s net.
Ohh yeah my bad! Haven’t seen the DDG notice. It’s not obvious and OP doesn’t give much info.
But I REALLY doubt this is AdgaurdVPN sending all those request, this would be a real concern for a lot of people and other VPNs would already have jumped on the “Adguard” is bad train.AdguardVPN seems effectively to send a lot of sketchy dns request…

it’s DDG that’s active, and which has filtered out these tracking requests sent by the adguard vpn android app (with its own vpn inactive) in the background.
Are there any nonmalicoius reasons why adguard would be dialing into ad servers? My first thought it that you gotta know who the advertisers are to block em, but I’m not familiar with adguard as a vpn or a browser side blocker.
yes, that’s my question too.
That’s crazy. I always recommend people to use self hosted Wireguard VPN. Installation is basically one command from github (autoinstaller script). Or use Mullvad VPN, it seems to be privacy-friendly.
This is something I’ve not understood yet. If you rent a server somewhere to use as a private VPN endpoint, your clear IP will be pretty much the only one connecting to the server. Correlating your traffic and your clear IP to your masked IP is easy for sufficiently motivated, able actors.
Meanwhile, the main benefit of a shared VPN such as Mullvad is that many users simultaneously use the same endpoint, making it much harder to identify the user (taking only IP and traffic into account), provided they don’t log your traffic.
So while having control over your endpoint is nice, how does that actually contribute anything meaningful to your privacy?
Mullvad knows exactly who is connecting, when they are connecting and where they are located. If you have payment information on file they also know your name and your credit card.
They can claim to somehow be “log free” but you can’t trust one who says they are going to not do something. Even if they aren’t abusing your data someone could of compromised them. Its not a good idea to place trust where you don’t have control.
Mullvad certifiably doesn’t log. Their VPN infrastructure even transitioned to RAM-only a few months back. They’ve been raided by the police and nothing was confiscated because there was nothing to confiscate. Obviously they have a list of registered accounts and payments, but without any connection to - well, connections.
I get what you mean though and mostly agree: There are only a few providers I trust enough to shift said trust from the ISP to them.
As mentioned in the comment you replied to: Yes, trusting a third party is a compromise. But you are also trusting a third party when renting a server for a private VPN endpoint, as well. A third party provider with probably a lot more logging going on than a trusted service such as Mullvad. While being way more exposed.
Since TOR isn’t feasible for most users 24/7, trusted commercial VPNs are the next best thing when the alternative is your ISP logging everything you do.
I disagree. You don’t control Mullvad VPN so you don’t control how the servers work. There is nothing Mullvad can do to change a fundamental property of the internet. They are no worse or better than your ISP. You shouldn’t use device provided by your ISP and using a VPN gives a company insight and sometimes control of your machine. You should use your own device on your own network. From there setup encrypted DNS and lock down your network.
What? So your advice for improving privacy is to not use a VPN, because the provider may log stuff and instead keep accessing stuff directly through your ISP who will log everything you do and simply use DNS over HTTPS/TLS, which does pretty much nothing for your privacy since your ISP still sees the servers you connect to?
That’s terrible advice.
Any possibility that these are apps or sites that you use while using that VPN? And maybe DDG is also blocking it? I don’t use any of that stuff so I’m just taking a guess.
i can see where you’re going with this but, no, these are not sites that i’ve visited. for example, my country has its own amazon domain and verizon does not operate where i live.
nope, this is all the adguard vpn android app on its own.
Users like this is exactly why you don’t need a VPN; you clearly have no understanding of how they work.
thanks for the feedback. i would be happy to hear what I’m presuming incorrectly here. always willing to learn and gain an understanding of how things do work.
Not op ( that guy was being intolerably rude ) but I’m not surprised that ddg is reporting that a vpn app is sending all these requests, the very nature of a VPN app is to capture and proxy all your traffic, so it will end up proxy all the tracking requests on your system. These likely came from a browser ( any site with an Amazon button for example will likely show as an amazing tracking hit )
In short, your VP is likely not selling your data.
i get what you’re saying, but the vpn was inactive when the app sent these requests. DDG was active at the time and using the VPN slot.
so it isn’t the vpn functionality, per se, of the app that’s doing anything here.
The problem with a VPN is that it isn’t a technology that’s designed to be private. It actually mainly was used for companies until recently.
When you use your VPN you are tunneling your traffic to someone else’s servers. They can see the same data your ISP can. Hopefully everything you do is encrypted but that is a discussion for another day. The point is that a VPN companies servers are no more trustworthy than the rest of the internet. You can’t control anything that leaves your device. That’s not how the internet was designed and it can’t be changed no matter how many claims a VPN company may make. Someone somewhere will always see you connect to the internet. At the end of the day you give up some privacy in exchange for your ability to use the internet.
In a nutshell, VPNs are mostly just snake oil
all good info. and all agreed. but the issue in this post isn’t the vpn functionality.
it’s what the adguard android app does in the background when the vpn, itself, is disconnected. that’s when these rogue requests were sent.
You’re wrong.
How exactly? Explain to me how your VPN can somehow make you anonymous. The backbone of the internet is decentralized which means someone somewhere will always see your traffic.
Who said anything about making you anonymous?